WUZEN-MYTHOS-EDITION is a web-based Android APK generation and control panel designed for security research. It positions itself as a modern replacement for legacy remote administration tools (RATs), with an emphasis on stealth, telemetry collection, and evasion techniques used in real-world mobile threat simulations. The project describes itself as “actively developed” and targets ethical hacking and penetration testing workflows—specifically those requiring rapid, customizable Android payloads. It is not a general-purpose app builder or development tool; its focus is narrow and operational.
What it does
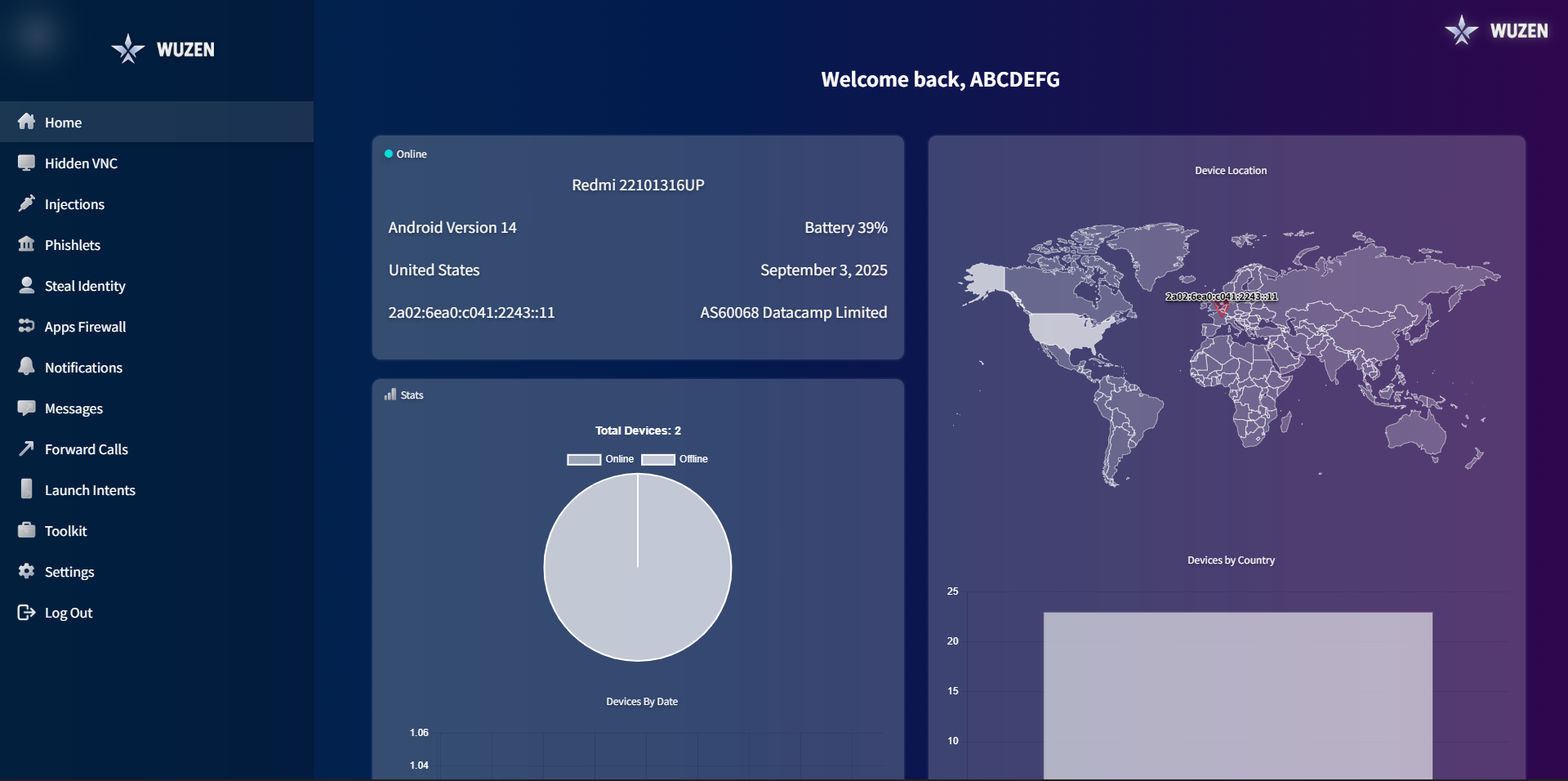
WUZEN provides a browser-accessible interface to configure and generate signed Android APKs without requiring Android Studio or manual Gradle builds. Key capabilities include:
- Telegram-based command and control: The generated APKs communicate with the panel via Telegram APIs, avoiding direct server dependencies
- HVNC and VNC support: Enables remote screen viewing and interaction (referred to as GHOST HVNC in the README)
- Telemetry and monitoring: Captures device information, call logs, SMS, notifications, installed apps, and location data
- Runtime injection and launch intent customization: Allows modifying how the APK starts and what background services or activities it triggers
- App firewall and call forwarding controls: Configurable per-payload rules for intercepting or redirecting calls and restricting app access
The panel runs on Linux, requires Node.js v24 LTS and OpenJDK 17+, and outputs APKs signed with a built-in keystore—no manual signing step is needed.
Getting it running
The project’s README outlines two installation paths: a recommended Quick Start and a Manual Setup. No Docker Compose file or docker run command appears in the provided context, and no shell commands are explicitly listed—only dependency badges and high-level instructions. Based on the stated prerequisites, a minimal local setup would involve:
git clone https://github.com/sunimakgoho-arch/WUZEN-MYTHOS-EDITION
cd WUZEN-MYTHOS-EDITION
npm install
# Ensure Java 17+ and Node.js 24 LTS are installed and in PATH
node server.js
The server starts a local web interface, accessible by default at http://localhost:3000. Login credentials are not specified in the provided excerpt—users would need to consult the config/ directory or environment variables, if documented elsewhere in the repository. The panel’s UI includes sections for dashboard telemetry, settings, firewall rules, HVNC/VNC toggles, injection payloads, and message routing.
Who this is for
This tool is intended for security professionals conducting Android-focused red team exercises, mobile threat emulation, or controlled penetration tests. It assumes familiarity with Android permission models, Telegram bot API setup (required for C2), and basic Linux system administration. Researchers who need repeatable, configurable APK generation—without maintaining Android build environments—may find value in the centralized panel. It is not intended for developers building legitimate apps, nor for beginners learning Android development. The emphasis on evasion, telemetry, and stealth places it firmly in the operational security toolkit, not education or prototyping.
How it compares
WUZEN shares functional overlap with other Android RAT frameworks such as AhMyth, AndroRAT, and DroidJack, but distinguishes itself through its web-based, Telegram-integrated architecture and lack of reliance on public cloud servers. Unlike AhMyth, which uses WebSocket-based C2 and requires manual APK compilation, WUZEN abstracts build steps into a visual interface and handles signing automatically. Compared to Termux-based payloads (e.g., using msfvenom or shad0w), WUZEN delivers a more self-contained, GUI-managed workflow—but at the cost of larger APK size and tighter coupling to its own infrastructure. It is heavier and more opinionated than minimal CLI tools like APKInjector or Drozer, and does not offer the same depth of runtime Android instrumentation.
The project’s GitHub page shows 201 stars, suggesting modest but active community interest. Its MIT license allows modification and redistribution, though users should note that building or deploying unauthorized remote control software on devices without consent violates laws in most jurisdictions—including the U.S. Computer Fraud and Abuse Act and the EU’s NIS2 Directive. The README includes no disclaimers about legal usage, and no documentation is visible in the provided excerpt regarding responsible disclosure, ethical boundaries, or compliance guidance.
WUZEN-MYTHOS-EDITION is a functional, dependency-specific tool for generating Android payloads with integrated telemetry and remote control—built for a narrow slice of the security research workflow. It is not a general-purpose development aid, nor is it suitable for production or unmonitored deployment. The source code and documentation are available at https://github.com/sunimakgoho-arch/WUZEN-MYTHOS-EDITION.
Comments