Active Directory red-team frameworks have become essential for security professionals assessing Windows domain environments. Tools like BloodHound for graphical attack-path mapping, CrackMapExec for remote execution, and PowerView for enumeration have long been staples. Each solves a piece of the puzzle, but integrating them can be cumbersome. A newer entrant, AdStrike, aims to consolidate these capabilities into a single, AI-powered platform for authorized penetration testing.
What AdStrike does differently
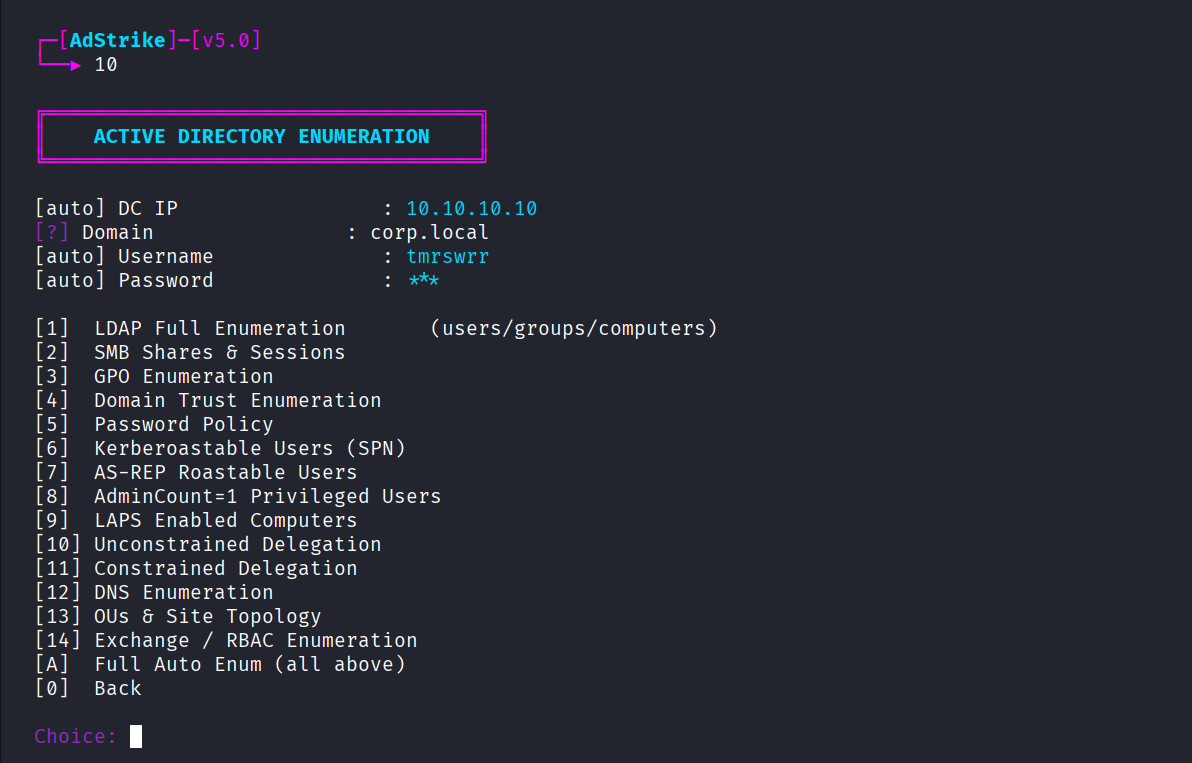
AdStrike distinguishes itself through a modular architecture that wraps several common red-team tasks into a unified pipeline. The framework emphasizes AI-driven assistance for AD enumeration, attack-path analysis, and Kerberos/ADCS workflows. Instead of switching between separate tools, operators can launch an enumeration module, feed its output into an attack-path analyzer, and then generate a report—all within the same Python environment. This integration reduces manual data transfer and context switching. The AI component is advertised to help prioritize targets and suggest exploitation steps, though specifics of the models are not disclosed in the repository. Reporting is built-in, producing structured outputs that can be customized, which saves time during post-engagement documentation. Automation features allow operators to script multi-step attack chains, making repeated tests more efficient. The entire framework is written in Python, which makes it accessible to those familiar with the language but may require additional setup for Windows-specific libraries.
Quick start
AdStrike is distributed as a Python project. You can get it running with these steps:
git clone https://github.com/capture0x/AdStrike.git
cd AdStrike
pip install -r requirements.txt
After installation, the main entry point is a command-line interface. Running python adstrike.py --help displays available modules and options. The project’s README includes basic usage examples, such as launching an initial enumeration or generating an attack-path graph.
Trade-offs
The primary advantage of AdStrike is its breadth. It combines enumeration, analysis, and reporting in one toolkit, which can simplify a red team’s toolchain. The modular design means individual components can be updated or replaced without rebuilding the whole system. The AI-powered suggestions, while not deeply explained, could accelerate decision-making for complex AD environments. Automation support is robust, allowing operators to create custom playbooks.
On the other hand, AdStrike is a young project with only 41 stars on GitHub, indicating a small user base. This means community support and third-party plugins are limited compared to established tools. Documentation appears sparse, so users may need to experiment to fully leverage the framework. Because it relies on Python, it inherits typical dependency challenges, especially for Windows-specific libraries like impacket or PyKCS11. Some operators may find the learning curve steep if they are not already comfortable with Python scripting. Finally, the AI features, while promising, lack transparency about underlying models, which could be a concern for teams requiring full control over decision logic.
Where it fits in your stack
AdStrike is best suited for red teams that want an all-in-one solution for Active Directory assessments and are willing to invest time in learning its nuances. It can serve as a central hub, replacing a collection of disparate scripts and tools. For organizations already standardized on Python, integration is straightforward. However, teams that rely heavily on mature, specialized tools like BloodHound may prefer to keep them separate. The framework’s automation capabilities make it attractive for handling repetitive engagements or building custom testing pipelines. If you’re looking for a modular, AI-assisted approach to AD red-teaming, the source is on GitHub.
Comments