Claude-OSINT provides two paired skills designed for the Claude skills system. Hosted on GitHub at elementalsouls/Claude-OSINT with 755 stars, the project uses Python and consists of drop-in SKILL.md files totaling around 5,500 lines of structured tradecraft. These skills transform Claude into an external reconnaissance operator suited for authorized red-team operations and bug bounty engagements. One skill, osint-methodology, covers strategic and procedural aspects like asset-graph discipline, severity rubrics, time budgeting, and deliverable templates. The other, offensive-osint, supplies tactical elements including probe paths, regex patterns, payloads, curl one-liners, and tool references.
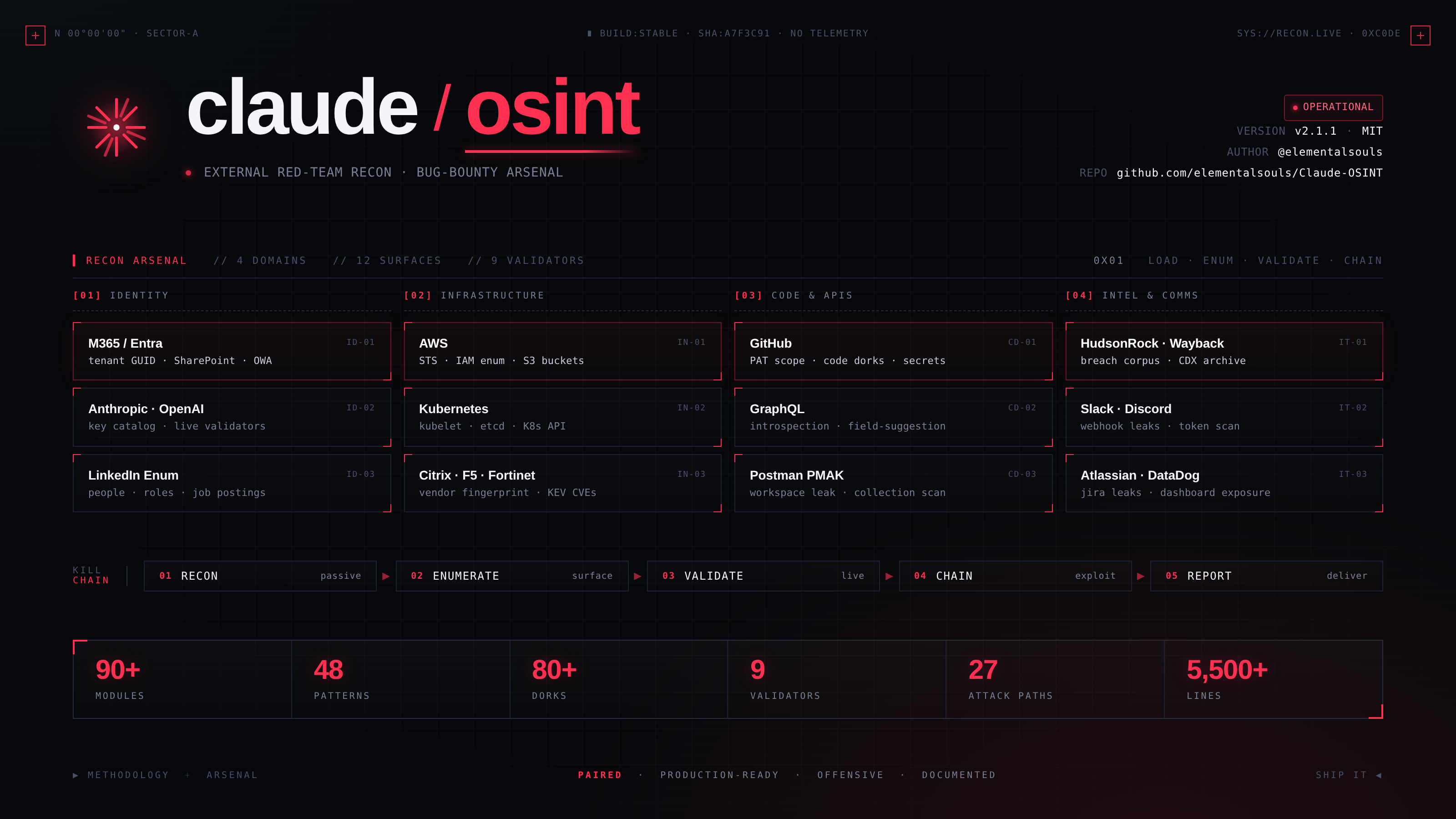
The project addresses gaps in AI-assisted reconnaissance by embedding expert-level knowledge directly into Claude's prompting. It includes 90+ recon modules, 48 secret-regex patterns, 80+ dorks, 9 read-only credential validators, and 27 attack-path templates. A self-evaluation with 32 prompts scores 96.9% pass rate, indicating broad coverage for the recon phase—around 85-90% of practitioner needs in authorized scenarios.
Core components
The repository organizes content into self-contained skill directories under skills/:
claude-osint/
├── skills/
│ ├── osint-methodology/SKILL.md # 1,694 lines: methodology focus
│ └── offensive-osint/
│ ├── SKILL.md # 4,168 lines: tactical arsenal
│ └── scripts/secret_scan.py # Stdlib-only secret scanner
├── docs/ # Architecture, coverage, install, usage
├── examples/ # Four end-to-end engagement examples
├── tests/smoke-test-prompts.md # 32-prompt evaluation
└── assets/banner.png
Claude loads these automatically when relevant phrases appear in conversations.
Capabilities span 12 domains, with examples from the skill index:
Reconnaissance & Asset Discovery
- Five-stage external recon pipeline with time-budget profiles (1 hour, 4 hours, 1 day, 1 week).
- Subdomain enumeration from crt.sh plus seven fallback sources.
- Common-prefix sweeps using 100+ prefixes via PowerShell and bash scripts.
- WHOIS, RDAP, historical WHOIS, and reverse-WHOIS pivots.
- Public records queries via OpenCorporates, SEC EDGAR, and others.
Identity & SSO Mapping
- Microsoft Entra tenant fingerprinting and GUID extraction.
- M365 enumeration including Teams federation and device-code phishing paths.
- Okta tenant slug discovery and user enumeration via
/api/v1/authn. - Generic OIDC support for Auth0, Keycloak, and similar.
- AWS account-ID extraction from headers using ARN regex.
Web Application Attack Surface
- Swagger/OpenAPI discovery across 28 paths.
- GraphQL introspection with 13 paths, field suggestions, and depth bypasses.
- Checks for 15 always-on paths like
.git,.env, and actuator endpoints. - Missing security headers audit (HSTS, CSP, XFO).
Additional assets include a secret_scan.py script for scanning with 48 regex patterns and read-only validators for credentials.
Getting it running
Setup requires the Claude skills system, detailed at docs.claude.com. Download the repository:
git clone https://github.com/elementalsouls/Claude-OSINT.git
Copy the skill directories to Claude's skills folder:
cp -r claude-osint/skills/osint-methodology ~/.claude/skills/
cp -r claude-osint/skills/offensive-osint ~/.claude/skills/
Claude detects and activates them on matching phrases, such as recon-related queries. No further dependencies are needed beyond Claude's environment—the skills are Markdown files, and secret_scan.py runs with standard Python libraries.
For testing, review tests/smoke-test-prompts.md or the four walkthroughs in examples/. The docs/ folder covers architecture, coverage details, and usage patterns.
Who this is for
Red-team operators and bug bounty hunters conducting authorized external reconnaissance benefit most. It suits practitioners needing structured guidance on asset discovery, identity mapping, and attack surface probing without leaving Claude's interface. Time-budgeted pipelines help during scoped engagements, like 1-hour sprints or week-long assessments.
Examples demonstrate full engagements: starting from a domain, building asset graphs, escalating via SSO pivots, and scoring findings. If your workflow involves Claude for brainstorming or automation, these skills add depth to recon phases. Teams with GenAI security research interests, like the project's creator ElementalSoul, may extend it for custom modules.
How it compares
Claude-OSINT integrates directly with Claude, differing from standalone OSINT tools like Amass (for subdomain enum) or Recon-ng (modular frameworks). It avoids command-line overhead by embedding curl one-liners, tool URLs, and dorks into prompts. For secret detection, its stdlib secret_scan.py is lighter than full scanners like TruffleHog, focusing on read-only validation.
Unlike general LLMs, the paired skills enforce scope discipline—staying external and authorized. Coverage overlaps tools like Sublist3r or Aquatone but packages them procedurally for AI use. Drawbacks include dependency on Claude's skills system and lack of active scanning; it's prompt-based, not a runner.
It's heavier on methodology than pure arsenal packs, with 1,694 lines dedicated to thinking frameworks versus tactical payloads. For non-Claude users, projects like OSINT Framework or SpiderFoot offer browserable modules without AI priming.
Claude-OSINT targets authorized use only and skips internal pivots or exploits. Those seeking automated scanners or broad pentesting suites might prefer Metasploit or Nuclei. Source at https://github.com/elementalsouls/Claude-OSINT.
Comments