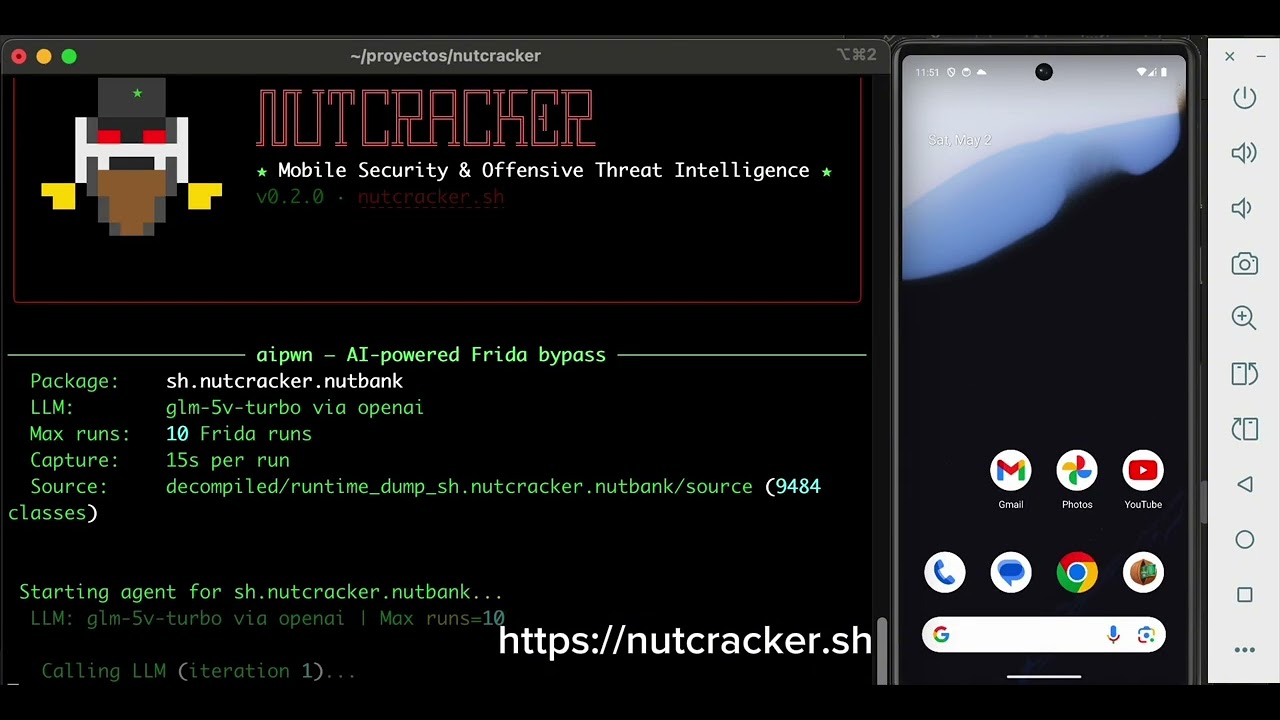
Nutcracker is a Python-based framework for Android app security analysis and offensive threat intelligence. Hosted at https://github.com/drneox/nutcracker with 18 stars, it targets protections like anti-root and RASP (Runtime Application Self-Protection) from vendors such as DexGuard, Arxan, Appdome, Promon, and RootBeer. The tool downloads apps, decompiles them, scans for hardcoded secrets and insecure configurations, and runs OSINT on extracted data. Version 0.2.0 beta aligns with MASVS standards for mobile app security verification, producing a consolidated PDF report. A demo video shows the workflow in action (https://youtu.be/nMcFy7ibgp0).
It addresses gaps in mobile pentesting by combining static and dynamic analysis in one pipeline. Users input a package name or APK URL, and Nutcracker handles downloading (via apkeep with AAS token, APKPure, or direct links), protection detection, deobfuscation, secret extraction, manifest checks, and recon on domains or leaks. An optional AI review filters false positives from LLM analysis.
Core features
Nutcracker bundles several analysis steps:
- APK/AAB downloading and installation: Pulls from Google Play, APKPure, or URLs; supports App Bundles with
adb install-multiplefor split APKs. - Protection detection and bypass: Identifies DexGuard, Arxan, Appdome, RootBeer, Promon Shield statically; uses Frida-based dynamic deobfuscation via
frida_server,gadget, orfart. - Secret and vulnerability scanning: Runs semgrep (OWASP MASTG rules), 38 internal regex patterns (
sast_scan), apkleaks, and gitleaks on decompiled code and APK; filters analytics SDKs like AppMetrica or AppsFlyer. - OSINT reconnaissance: Checks package IDs, domains, endpoints, and secrets via crt.sh for subdomains, plus public leaks on GitHub, Postman, FOFA, Shodan, Wayback; optional web searches.
- Reporting and filtering: Generates a technical PDF; applies optional LLM false positive filter (
ai-review).
These run modularly, with Frida Gadget as a fallback for instrumentation.
Getting it running
The project requires Python 3.11+ and targets Android analysis, integrating tools like Frida for dynamic work and apkeep for downloads. Clone the repo from GitHub:
git clone https://github.com/drneox/nutcracker
cd nutcracker
Install dependencies via pip, including apkeep, semgrep, apkleaks, gitleaks, and Frida tools—full list in requirements.txt or setup files. Set up an Android environment with adb for installation and frida_server on a rooted device or emulator. Configure pipelines in the tool's settings for deobfuscation (e.g., frida_server, gadget).
Run with a package name:
python nutcracker.py -p com.example.app
Enable OSINT with flags like --osint or --ai-review. For AABs, it detects splits automatically. MIT-licensed, last commit visible on the repo badges. The website https://nutcracker.sh provides more config details. Test on authorized apps only, per the legal disclaimer: use for owned apps, pentests with permission, or education—unauthorized scans risk legal issues.
Who this is for
Security researchers and pentesters analyzing Android apps benefit most. It suits teams checking MASVS compliance, hunting secrets in decompiles, or mapping threat intel from endpoints. For example, input a target package, and it flags RootBeer checks, pulls crt.sh subdomains, and scans for GitHub leaks in one pass—ideal for red team reports.
Educational users can study protections like Promon Shield or DexGuard obfuscation. If your workflow involves Frida scripting or semgrep rules, Nutcracker automates the chain. Not for casual reverse engineering; it assumes familiarity with ADB, rooted setups, and tools like apkleaks.
How it compares
Nutcracker stands out for its all-in-one approach versus siloed tools. Apkeep handles downloads alone, while MobSF offers broader static analysis but lacks built-in RASP bypass or OSINT. FridaTrace or objection cover dynamic instrumentation, yet Nutcracker pipelines them with gadget fallback and secret scanners.
For secrets, apkleaks or gitleaks run standalone; here, they're augmented with 38 regex rules and manifest checks. OSINT modules echo tools like EyeWitness or Aquatone but tie directly to app artifacts, querying FOFA/Shodan/Wayback. Heavier than lightweight scripts (e.g., RootBeer detector repos), it requires more setup but outputs PDFs ready for clients. No direct 1:1 alternative matches the beta's beta scope—18 stars reflect its niche, early stage.
At 0.2.0 beta, Nutcracker fits researchers needing integrated Android analysis but skips beginners without Frida experience or those avoiding dynamic setups. Source at https://github.com/drneox/nutcracker; check issues for updates.
Comments