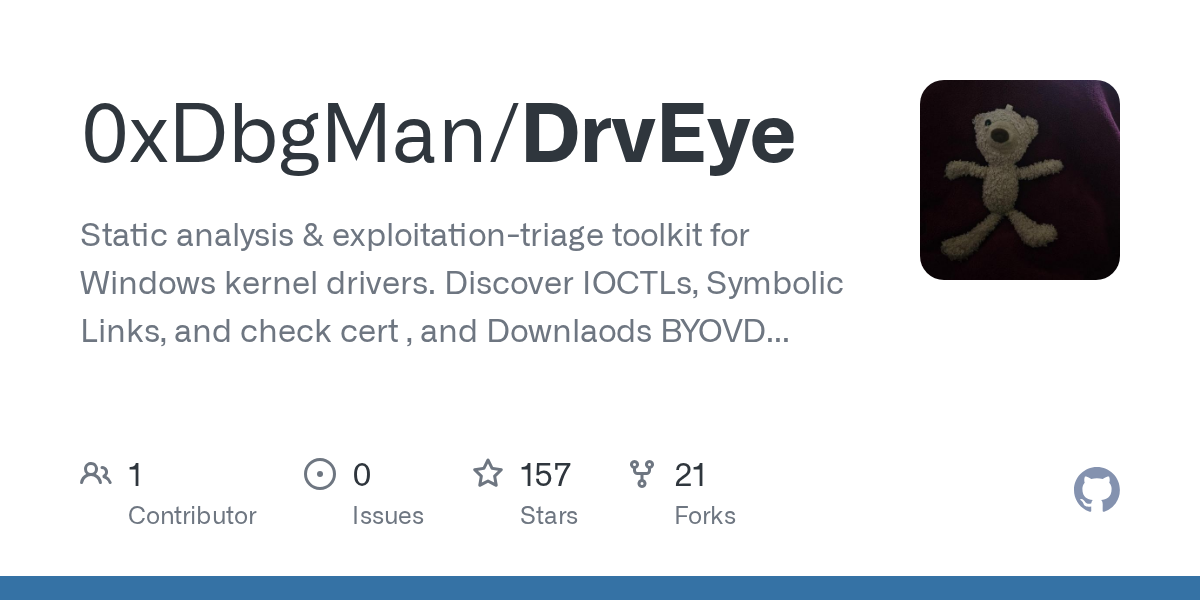
This project, DrvEye, offers a focused approach to analyzing Windows kernel drivers. It enables users to explore IOCTLs, symbolic links, and certification checks through a streamlined interface. Developers and researchers can leverage its tools to understand low-level driver interactions without complex configurations. The toolkit is written in Python and is available on GitHub for easy access.
Installing the project requires setting up dependencies that typically include standard build tools. The setup process involves a clear command structure that guides users through initial configuration. For those looking for a hands-on example, the provided code demonstrates how to integrate DrvEye into a testing environment.
One of the key features is its ability to handle static analysis tasks, making it valuable for debugging and maintaining driver integrity. Advanced users can explore deeper functionalities such as exploit triage and certification verification. If you're working on a project that demands precision in driver evaluation, DrvEye stands out as a practical choice.
The software is designed for technical teams who want to streamline their driver testing workflow. It avoids unnecessary overhead, focusing instead on core analysis tasks. For more information, you can review the project details at DrvEye GitHub. This resource offers a direct link to the source code and documentation.
When deciding whether to use DrvEye, consider the need for detailed driver insights versus broader application scope. It is most effective when paired with other tools for a comprehensive analysis. The flexibility of its setup makes it suitable for both newcomers and experienced developers.
The project emphasizes clarity and efficiency, offering a structured path to master kernel driver diagnostics. Its simplicity in design contrasts with heavier frameworks, making it accessible for targeted use cases. Explore the DrvEye repository to see how it integrates into existing workflows.
Comments