Android remains the most widely deployed mobile operating system globally, which makes it a persistent target for security researchers, pentesters, and bug bounty hunters. The tooling landscape is crowded, but many solutions are either GUI-heavy, bloated with unnecessary modules, or locked behind commercial licenses. For anyone doing authorized security assessments on Android devices, there's a real need for lightweight, scriptable tools that don't get in the way.
Enter DroidHunter
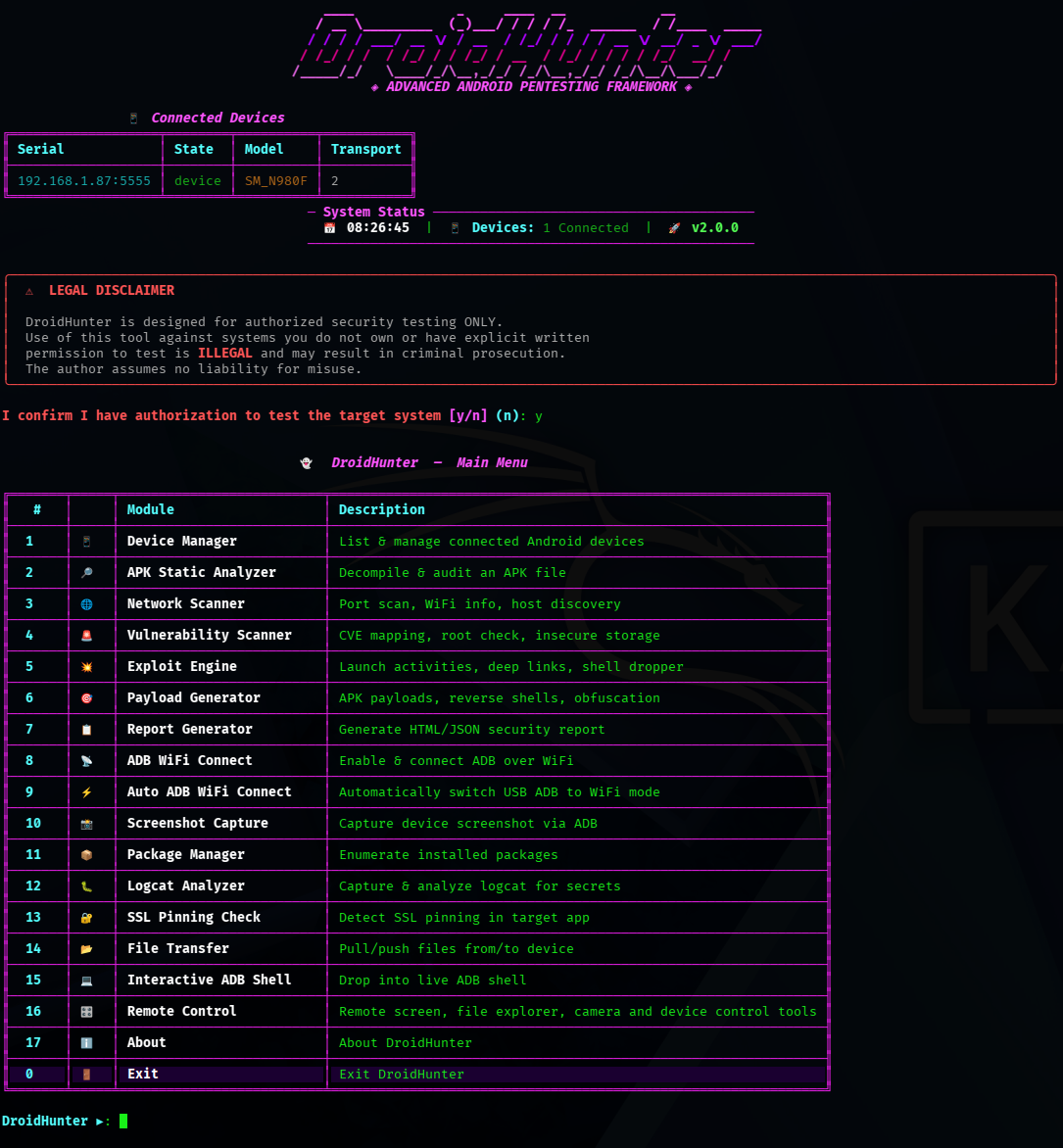
DroidHunter is a CLI-based Android security assessment framework built for authorized testing. It's a Python project that consolidates several common assessment workflows into a single command-line interface, reducing the need to juggle multiple standalone tools during an engagement.
What it brings to the table is breadth of function rather than depth in any single niche. ADB device management, APK analysis, network checks, vulnerability scanning, reporting, and remote control utilities are all housed under one roof. That's useful for testers who want to move quickly between tasks—pull an APK, scan it, check the device's network posture, and generate a report without switching contexts across five different applications.
The project sits at 44 stars on GitHub, which signals it's still in the early-adoption stage. That's worth noting: the community around it is small, and contributors should expect to read source code directly rather than rely on extensive documentation or community-maintained wikis.
Under the hood
DroidHunter is written in Python. The exact dependency list isn't specified in the project's seed information, but given the feature set—ADB interaction, APK parsing, network diagnostics—it almost certainly leans on libraries like adb bindings, androguard or similar APK analysis tools, and standard networking utilities. The CLI-driven architecture means it can be scripted and integrated into larger automated pipelines, which is a practical advantage for repeatable assessments.
The framework is structured around distinct functional areas. ADB device management handles the connection and interaction with physical or emulated Android devices. APK analysis targets the inspection of application packages for suspicious or vulnerable patterns. Network checks evaluate the device's connectivity and exposure surface. Vulnerability scanning attempts to identify known weaknesses, and the reporting module aggregates findings into usable output. Remote control tools extend the framework's reach beyond local device interaction.
None of these modules are described in granular detail in the available project metadata, so anyone considering DroidHunter for real work should inspect the source directly to understand exactly what each component does and where its limitations lie. That's standard practice for low-star open-source security tools, but it's especially important here given the sensitive nature of security assessment.
Getting it running
The project is hosted on GitHub and can be cloned directly. From there, Python-based installation is the expected path:
git clone https://github.com/hexsecteam/DroidHunter.git
cd DroidHunter
pip install -r requirements.txt
python droidhunter.py
The exact commands may vary depending on how the project structures its entry point and dependency management, so checking the repository's README for the most current instructions is advisable. Since it's Python-based, it should run on any platform where Python and ADB are available—Linux, macOS, and Windows are all viable.
Honest take
DroidHunter is a reasonable consolidation of Android assessment tasks into a single CLI tool, and it's clearly aimed at practitioners who prefer terminal-driven workflows. It's lighter than commercial alternatives and broader than single-purpose scripts. However, at 44 stars and with a small contributor base, it hasn't reached the maturity of established projects in this space. Anyone using it for real assessments should audit the code themselves and not assume that "scanning" modules are exhaustive or up to date with the latest CVE databases. It's a tool with a clear vision and a long way to go in execution. The source is on GitHub.
Comments