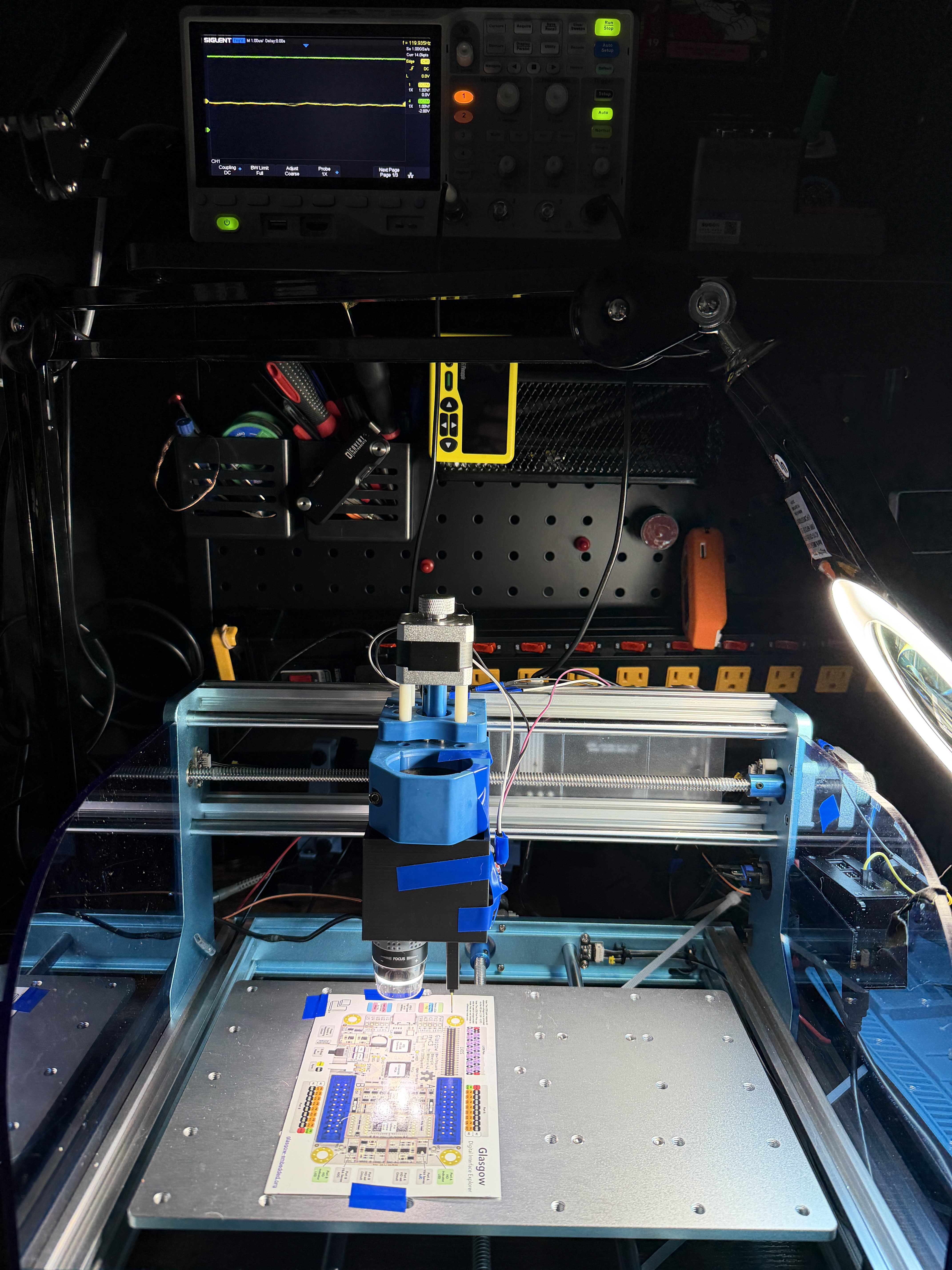
AutoProber automates flying probe testing for hardware hackers. The project, hosted at GainSec/AutoProber, runs on Python and has earned 299 GitHub stars. It equips AI agents or operators to handle tasks from initial target detection on a plate to precise pin probing. The stack integrates microscope imaging, CNC motion control, safety monitoring via oscilloscope, and a web dashboard for review.
This setup addresses the manual tedium and risk in hardware reverse engineering. Operators often juggle microscopes, CNC machines, probes, and scopes by hand. AutoProber sequences these steps: locate the target, map features like pads and chips, propose probe points, allow approval, then execute under safety checks. A demo video shows the process in action at gainsec.com/autoprober-demo-mp4. The full details appear on the project's site at gainsec.com.
Core workflow
AutoProber follows a defined sequence for agent-driven or manual operation:
- Ingest the project details into the agent.
- Connect hardware: GRBL CNC, USB microscope, Siglent oscilloscope, optical endstop.
- Verify all components function.
- Perform homing and calibration.
- Attach probe and microscope header.
- Signal a new target; it captures XYZ positions while labeling pads, pins, and chips.
- Stitch frames into an annotated map.
- Present probe targets on the dashboard for approval.
- Probe approved points and log results.
Control happens via the web dashboard, Python scripts, or directly by the agent. Dashboard panels show manual overrides, hardware status, map views, and probe queues.
Repository structure
The repository provides everything needed for a self-contained build:
apps/ Operator-facing scripts and Flask dashboard entrypoint
autoprober/ Reusable Python package for CNC, scope, microscope, logging, safety
dashboard/ Single-page web dashboard
docs/ Architecture, device references, operations, and safety guidance
cad/ Printable STL files for the current custom toolhead
config/ Example environment/configuration files
AGENTS.md Agent/operator safety rules
LICENSE PolyForm Noncommercial 1.0.0 license and commercial contact
pyproject.toml Python project metadata
uv.lock Locked Python dependency resolution
Download CAD files from cad/ for 3D printing the custom toolhead. Configuration examples in config/ cover lab-specific settings like device addresses. Documentation in docs/ includes safety.md, operations.md, and a bill of materials at BOM.md.
Hardware requirements
AutoProber relies on specific, tested components:
- GRBL-compatible 3018-style CNC controller over USB serial for motion.
- USB microscope streamed via
mjpg_streamer. - Siglent oscilloscope over LAN/SCPI: Channel 4 for safety endstop monitoring, Channel 1 for measurements.
- Optical endstop on a 5V supply to oscilloscope Channel 4.
- Optional network-controlled outlet for power cycling.
Reference parts include an optical endstop from Amazon listings used in the prototype. Check docs/ for defaults and adjust for your setup. Print toolhead parts from cad/ STL files.
Safety model
Physical motion demands caution. AutoProber treats the system as industrial machine control, not a standard web app. Key rules:
- Ignores GRBL
Pn:Pprobe pin; relies on oscilloscope Channel 4 for endstop. - Monitors Channel 4 continuously during motion.
- Stops on Channel 4 trigger, voltage ambiguity, CNC alarm, or X/Y/Z limits.
- No automatic recovery; agent or operator must intervene.
Review AGENTS.md for agent-specific rules. First-time users must read safety and operations docs before powering on.
Getting it running
Clone the repository from GitHub:
git clone https://github.com/GainSec/AutoProber.git
cd AutoProber
It uses Python with pyproject.toml and uv.lock for dependencies. Install uv if needed (pip install uv), then lock and sync:
uv sync
The autoprober/ directory forms the core Python package. Run the Flask dashboard from apps/, which serves the single-page app in dashboard/. Connect hardware per config/ examples: USB for CNC and microscope, LAN for scope. Set environment variables for your device paths, like serial ports or SCPI IPs.
Start the dashboard:
cd apps
flask run
Access at http://localhost:5000. From there, connect devices, home the CNC, calibrate, and process targets. Scripts in apps/ allow scripted control. Test without hardware first using docs for simulation notes. Full operations in docs/operations.md.
Who this is for
Hardware hackers probing chips, boards, or unknown devices will find it useful. It suits reverse engineers automating pin discovery and electrical measurements, especially with AI agents directing the flow. Labs with GRBL CNCs and basic scopes can adapt it quickly. If you sequence microscope scans with safe probing, this stack handles the integration.
Small teams or individuals building custom test jigs benefit from the open CAD and Python layers. The PolyForm Noncommercial 1.0.0 license fits hobbyists and non-commercial research; contact GainSec for commercial use.
Comparisons to alternatives
Commercial flying probe testers like those from SPEA or Takaya cost tens or hundreds of thousands and target high-volume PCB assembly. AutoProber runs on hobby-grade hardware under $1,000, trading precision for affordability and agent extensibility. Manual setups with OpenCV on a microscope plus GRBL sender require custom scripting; this project packages it with safety and dashboard.
Open-source CNC tools like FluidNC or TinyG can replace GRBL, but lack the integrated scope monitoring and probe review. For pure imaging, projects like OctoPrint add web control to microscopes, but stop short of motion safety.
AutoProber demands hardware assembly and safety diligence, so it's not for software-only users or those without lab space. Source code, docs, and demo at github.com/GainSec/AutoProber.
Comments